Blockchain security software refers to a category of tools and technologies designed to enhance the security of blockchain networks and applications. These software solutions address various security challenges faced by decentralized systems, such as data integrity, confidentiality, authentication, and authorization.
Key features of blockchain security software include:
- Encryption: Blockchain security software often uses cryptographic algorithms to encrypt data, ensuring that sensitive information remains confidential and secure.
- Digital Signatures: Digital signatures are used to verify the authenticity of transactions and messages on the blockchain, preventing unauthorized modifications and ensuring data integrity.
- Access Control: Blockchain security software implements access control mechanisms to manage user permissions and restrict unauthorized access to sensitive data and resources.
- Consensus Mechanisms: Consensus algorithms are integral to blockchain security, as they ensure that all nodes in the network agree on the validity of transactions. This prevents malicious actors from manipulating the blockchain’s history.
- Smart Contract Security: For blockchain platforms that support smart contracts, security software helps identify and mitigate vulnerabilities in the contract code to prevent exploits and attacks.
- Key Management: Secure key management solutions are essential for protecting private keys used to sign transactions and access blockchain assets. Blockchain security software helps manage these keys securely.
- Auditing and Monitoring: Continuous auditing and monitoring tools help detect and respond to security threats and anomalies in real-time, enhancing the overall security posture of the blockchain network.
- Secure Wallets: Blockchain security software includes secure wallet solutions for storing cryptocurrencies and other digital assets, protecting them from theft and unauthorized access.
Overall, blockchain security software plays a crucial role in ensuring the integrity, confidentiality, and availability of blockchain networks, making them more resilient against cyber threats and attacks.
Blockchain security software is like a digital guardian that protects the integrity and privacy of transactions recorded on a blockchain. Picture a shared notebook where everyone writes down transactions, but instead of relying on trust, blockchain security software uses advanced tools to keep things secure.
Encryption, for instance, scrambles the messages in the notebook so that only those with the right “key” can understand them, safeguarding sensitive information from prying eyes. Digital signatures act like electronic stamps next to each entry, ensuring that everyone knows who made each transaction and that it’s genuine.
Access control functions like a lock on the notebook, allowing only authorized users with the correct permissions to make changes or view certain parts of the ledger. This helps prevent unauthorized tampering or snooping.
Consensus mechanisms are akin to a group vote before adding a new transaction to the notebook. Everyone must agree that a transaction is valid before it’s accepted, preventing any single person from making fraudulent entries.
Together, these features form the backbone of blockchain security software, protecting the integrity and confidentiality of data on the blockchain network.
Also Read ➤ ➤ 9 Must Watch Blockchain Videos For Beginners (Free)
What are the common security risks associated with blockchain?
Common security risks associated with blockchain include 51% attacks, where a single entity gains control of the majority of the network’s computing power, as well as smart contract vulnerabilities, where flaws in the code can be exploited to steal funds or disrupt operations.
What is encryption in blockchain security?
Encryption in blockchain security involves converting plaintext data into ciphertext using cryptographic algorithms. This ensures that sensitive information stored on the blockchain remains confidential and secure, as only authorized parties with the decryption key can access the original data.
How do digital signatures contribute to blockchain security?
Digital signatures are used in blockchain to verify the authenticity and integrity of transactions. Each transaction is signed with a unique digital signature, which proves that it was created by the rightful owner of the associated cryptographic key and has not been altered since it was signed.
What role do consensus mechanisms play in blockchain security?
Consensus mechanisms ensure that all nodes in a blockchain network agree on the validity of transactions and the state of the ledger. By requiring network-wide agreement before adding new blocks to the blockchain, consensus mechanisms prevent malicious actors from tampering with the transaction history.
How can smart contract security be improved in blockchain applications?
Smart contract security can be improved by conducting thorough code audits and testing for vulnerabilities before deploying smart contracts on the blockchain. Additionally, implementing best practices such as input validation, access control, and fail-safe mechanisms can help mitigate the risk of exploits and attacks.
What steps can organizations take to enhance blockchain security?
Organizations can enhance blockchain security by implementing robust access controls, regularly updating software to patch known vulnerabilities, educating users about security best practices, and partnering with reputable security firms to conduct audits and assessments of their blockchain infrastructure.
Also Read ➤ ➤ Binance Chain vs Binance Smart Chain
The Main Agenda – Best Blockchain Security Software
Chainalysis

Chainalysis is a blockchain security software renowned for its comprehensive suite of tools designed to combat illicit activities and ensure compliance with regulations. With its advanced analytics platform, Chainalysis enables organizations, including law enforcement agencies and financial institutions, to track and trace cryptocurrency transactions across various blockchain networks.
One unique aspect of Chainalysis is its ability to provide insights into the flow of funds and identify suspicious behavior, such as money laundering and fraud, thereby enhancing the overall security of the blockchain ecosystem. Pros include its user-friendly interface and extensive database of blockchain data, empowering users to make informed decisions about risk management and regulatory compliance. However, Chainalysis has faced criticism for its potential impact on user privacy and civil liberties, raising concerns about the balance between security and individual rights.
Forta

Forta stands out as a blockchain security software solution focused on protecting decentralized finance (DeFi) protocols and smart contracts from vulnerabilities and attacks. By offering real-time monitoring and automated threat detection capabilities, Forta helps DeFi projects identify and mitigate security risks before they can be exploited by malicious actors.
One unique point of Forta is its emphasis on proactive security measures, including bug bounties and security audits, to prevent potential breaches and ensure the safety of users’ funds. Pros include its specialized focus on DeFi security and its ability to adapt to the evolving threat landscape, providing continuous protection against emerging risks. However, Forta’s effectiveness may be limited by the complexity of DeFi protocols and the rapid pace of innovation in the blockchain space, requiring constant updates and improvements to maintain security.
Also Read ➤ ➤ Top paid cryptocurrency and blockchain courses
Trail of Bits

Trail of Bits offers a comprehensive suite of blockchain security services, including smart contract audits, penetration testing, and security assessments, to help organizations identify and mitigate vulnerabilities in their blockchain applications. With its team of experienced security researchers and engineers, Trail of Bits conducts in-depth analyses of smart contract code and blockchain protocols to uncover potential weaknesses and recommend remediation measures.
One unique aspect of Trail of Bits is its commitment to open-source security tools and contributions to the blockchain community, such as the creation of Manticore, a symbolic execution tool for analyzing smart contracts. Pros include its technical expertise and track record of delivering high-quality security assessments, instilling confidence in clients’ blockchain deployments. However, Trail of Bits’ services may be cost-prohibitive for small or early-stage blockchain projects, limiting access to its expertise for startups and developers with limited resources.
Hacken
Hacken is a blockchain security software company known for its comprehensive range of cybersecurity services tailored to the blockchain and cryptocurrency industry. With a focus on proactive threat detection and incident response, Hacken offers solutions such as penetration testing, vulnerability assessments, and security audits to help organizations identify and mitigate security risks in their blockchain infrastructure.
One unique point of Hacken is its decentralized approach to cybersecurity, leveraging a global network of white-hat hackers and security experts to provide round-the-clock monitoring and support. Pros include its extensive expertise in blockchain security and its commitment to transparency and ethical hacking practices, fostering trust and confidence among clients. However, Hacken’s services may be geared towards larger enterprises and organizations with substantial security budgets, potentially limiting access for smaller startups and projects.
Also Read ➤ ➤ Blockchain Interoperability
Quantstamp
Quantstamp is a blockchain security firm specializing in automated smart contract auditing and security solutions. Leveraging advanced static and dynamic analysis techniques, Quantstamp helps organizations identify and remediate vulnerabilities in their smart contract code, reducing the risk of exploits and attacks.
One unique aspect of Quantstamp is its scalable auditing platform, which can analyze smart contracts across multiple blockchain platforms, including Ethereum, Binance Smart Chain, and others. Pros include its fast and efficient auditing process, enabling organizations to quickly identify and address security issues in their smart contracts before deployment. However, Quantstamp’s services may be limited by the complexity of smart contract code and the evolving nature of blockchain security threats, requiring ongoing vigilance and updates to maintain effectiveness.
Securify
Securify is an open-source security tool designed to analyze and detect security vulnerabilities in Ethereum smart contracts. Developed by researchers at ETH Zurich, Securify uses a combination of static analysis and symbolic execution techniques to identify potential security flaws, such as reentrancy bugs and integer overflows, in smart contract code.
One unique point of Securify is its focus on formal verification, allowing developers to mathematically prove the correctness of their smart contracts and ensure compliance with security best practices. Pros include its ease of use and integration with popular development tools, making it accessible to developers of all skill levels. However, Securify’s effectiveness may be limited by its reliance on static analysis techniques, which may not capture all possible security vulnerabilities in complex smart contracts.
Also Read ➤ ➤ Blockchain Technology and Crypto Vocabulary
Mythrill
Mythril is a security analysis tool for Ethereum smart contracts, designed to identify and mitigate security vulnerabilities that could lead to exploits or attacks. With its user-friendly interface and powerful analysis engine, Mythril helps developers identify potential security issues in their smart contract code, such as reentrancy bugs, integer overflows, and logic errors.
One unique aspect of Mythril is its support for both symbolic execution and symbolic testing, allowing developers to explore different execution paths and identify hidden vulnerabilities. Pros include its versatility and flexibility, making it suitable for both beginners and experienced developers. However, Mythril’s effectiveness may be limited by its reliance on static analysis techniques, which may not capture all possible security vulnerabilities in complex smart contracts.
Manticore
Manticore is a symbolic execution tool developed by Trail of Bits for analyzing smart contracts and blockchain protocols. With its advanced analysis capabilities, Manticore helps developers identify security vulnerabilities and design flaws in their smart contract code, such as integer overflows, buffer overflows, and logic errors.
One unique point of Manticore is its support for both symbolic execution and concrete execution, allowing developers to explore different execution paths and identify potential attack vectors. Pros include its scalability and efficiency, enabling developers to analyze large and complex smart contracts with ease. However, Manticore’s effectiveness may be limited by its complexity and the expertise required to use it effectively, potentially posing challenges for developers with limited experience in symbolic execution and security analysis.
Also Read ➤ ➤ Blockchain Interview Questions Part -1
Slither
Slither is a static analysis tool developed by Crytic for detecting security vulnerabilities in Ethereum smart contracts. With its comprehensive set of checks and rules, Slither helps developers identify potential security issues in their smart contract code, such as reentrancy bugs, uninitialized storage variables, and function visibility vulnerabilities.
One unique aspect of Slither is its integration with popular development environments, such as Truffle and Remix, making it easy for developers to incorporate security analysis into their existing workflows. Pros include its ease of use and accessibility, making it suitable for developers of all skill levels. However, Slither’s effectiveness may be limited by its reliance on static analysis techniques, which may not capture all possible security vulnerabilities in complex smart contracts.
Oyente
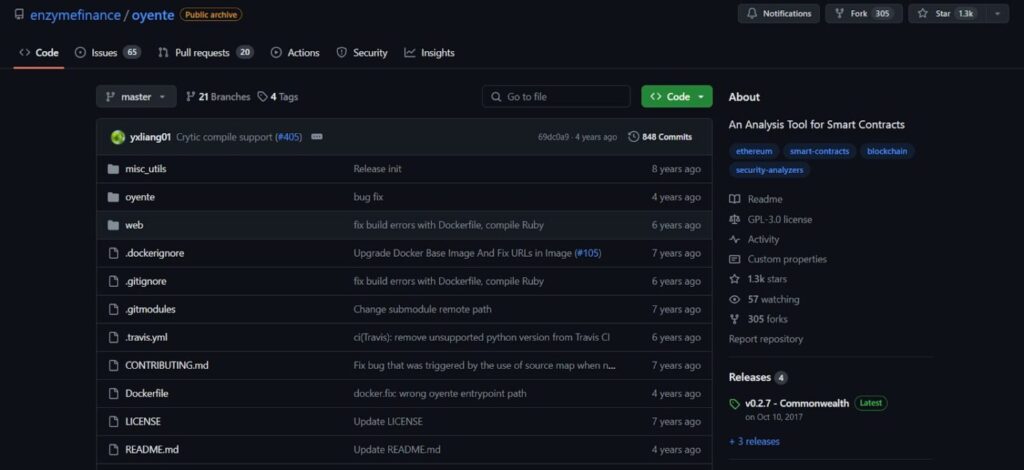
Oyente is an open-source security analysis tool specifically designed for Ethereum smart contracts. Developed by researchers at Enzyme Finance, Oyente employs static analysis techniques to detect potential security vulnerabilities in smart contract code, such as reentrancy bugs, integer overflows, and gas limit vulnerabilities.
One unique aspect of Oyente is its ability to simulate potential attack scenarios and identify possible exploit paths, allowing developers to assess the security posture of their smart contracts comprehensively. Pros include its accessibility and ease of use, making it suitable for developers of all skill levels. However, Oyente’s effectiveness may be limited by its reliance on static analysis techniques, which may not capture all possible security vulnerabilities in complex smart contracts.
Also Read ➤ ➤ The Architecture of Blockchain Technology
Conclusion
In summary, these blockchain security software solutions play crucial roles in ensuring the safety and integrity of blockchain networks and applications. While each tool has its unique features and strengths, they collectively contribute to the ongoing effort to enhance blockchain security and protect users from potential threats and vulnerabilities. However, it’s essential for developers and organizations to understand the capabilities and limitations of each software solution and employ best practices to mitigate security risks effectively.