Key Takeaways:
- Solana’s Cross-Chain Bridge Wormhole was exploited and 120,000 ETH (about $323 million) hacked.
- According to our sources the attacker gets 120,000 ETH in the first place from an earlier transaction.
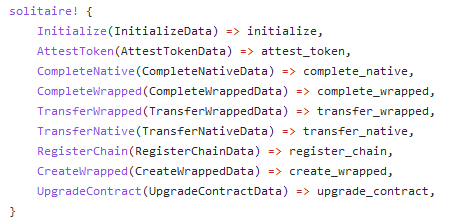
- The version of
solana_programthat Wormhole used didn’t verify the address being used.
Today morning Wormhole informed people that the wormhole network was exploited for 120k wETH. ETH will be added over the next hours to ensure wETH is backed 1:1. They are working to get the network back up quickly. The protocol’s official website is currently offline. Wormhole Portal is a platform that helps users transfer cryptocurrency between the Solana and Ethereum blockchains. This is the largest crypto hack of 2022 so far. The Wormhole team has offered a $10M bug bounty for the return of the funds.
According to our sources, a quick check of the encoded VM that the attacker submitted showed that it contained valid signatures from the guardians. This meant that either they got the private keys, or they exploited the bridge. Given that the attackers had leftover $600MM in tokens in the bridge, we figured out that the latter was more likely. Sure enough, there was a corresponding transaction on Solana where the attacker bridged out the ETH.
The attacker gets 120,000 ETH in the first place from an earlier transaction. Our sources checked Wormhole’s GitHub and determined that they must have called the complete_wrapped function. But the complete_wrapped function requires a valid VAA. How did the attacker generate a VAA account that the bridge would accept? When our sources checked the VAA account that the attacker used, they found that it had been created in an even earlier transaction. Specifically, in this transaction, the attacker called post_vaa on the main Wormhole bridge.
Then our sources figured out how the attacker managed to bypass the signature checks that post_vaa performs. Well, the attacker provided a SignatureSet which was created in yet another transaction. This one is called verify_signatures on the main bridge. The verify_signatures function is meant to take a set of signatures provided by the guardians and pack it into a SignatureSet. But it doesn’t actually do any of the verification itself. Instead, it delegates that to the Secp256k1 program.
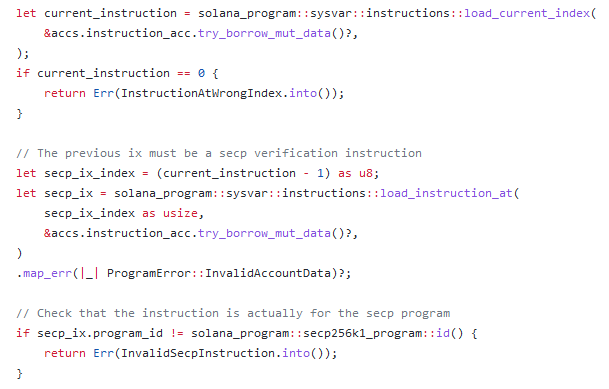
The problem starts from here. The `solana_program::sysvar::instructions` mod is meant to be used with the Instructions sysvar, a sort of precompile on Solana. However, the version of `solana_program` that Wormhole used didn’t verify the address being used. This means that you could create your own account which stored the same data that the Instructions sysvar would have stored, and substituted that account for the Instruction sysvar in the call to verify_signatures. This would essentially bypass signature validation entirely.
Hours earlier, the attacker created this account which contained a single serialized instruction corresponding to a call to the Secp256k1 contract. Then they passed in that account as the Instruction sysvar. Once they had the fake SignatureSet, it was trivial to use it to generate a valid VAA and trigger an unauthorized mint to their own account. The rest is history. Wormhole didn’t properly validate all input accounts, which allowed the attacker to spoof guardian signatures and mint 120,000 ETH on Solana, of which they bridged 93,750 back to Ethereum.
In a Reddit post in January, Ethereum co-founder Vitalik Buterin predicted that bridges would be unpopular in the future, citing risks to the backing of bridged assets.