Key Takeaways:
- Qi Dao informed their users that superfluid’s vesting contract for QI has been exploited.
- User funds on QiDao contracts are safe.
- The exploit is solely on Superfluid.
- QI bridging is temporarily paused.
Today Qi Dao informed their users that superfluid’s vesting contract for QI has been exploited. User funds on QiDao contracts are safe. The exploit is solely on Superfluid. Soon after informing about the exploit, QI gave a quick update.
QI informed that all funds in QiDao are safe and no user funds have been affected. But they are aware there are other tokens affected. QI bridging is temporarily paused. QiDAO faced an exploit on its Superfluid vesting contract which lead to a 65% drop in the price of the governance token QI. QI price fell from $1.24 to $0.18.
Superfluid confirmed the exploit on QiDAO. According to Superfluid today at 6.48 am GMT they were notified of a potential exploit of the QiDAO vesting contract. The contract leverages Superfluid code. Superfluid is investigating the incident and will update people accordingly. The protocol enables users to move assets on-chain in a constant flow in real-time from one wallet to another.
Superfluid is investigating a potential protocol layer exploit. As a precaution, they request people to unwrap all their SuperTokens. The attackers might be targeting wallets/contracts with large amounts.
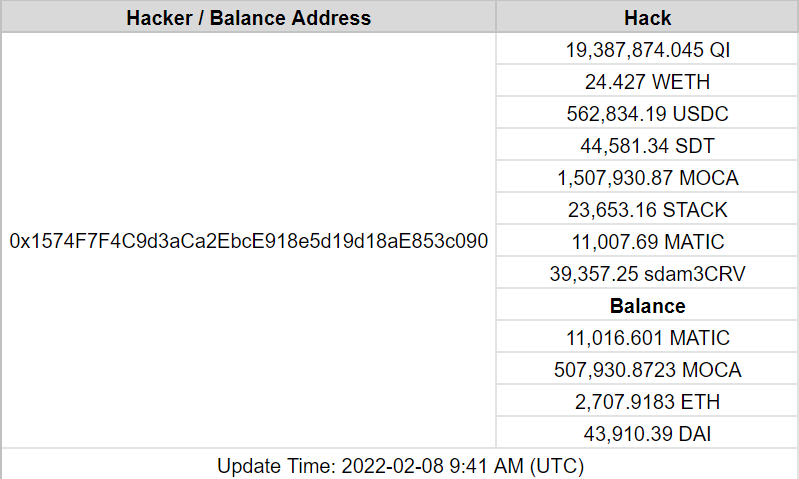
While there was no impact on the user’s funds, the hackers responsible for the attack were able to escape with $20 million in tokens, including 24 WETH, 562,000 USDC, 44 SDT, 1.5 million MOCA, 23,000 STACK, and nearly 40,000 sdam3CRV. According to early reports, the stolen funds belonged to some of the project’s early backers and included team vested tokens as well.
SlowMist created a fund tracker that shows the balance of each stolen token. They estimated that the hackers stole about $13 million in cryptocurrencies after analysing the wallet transaction data. After SlowMist analysis, the attackers exchanged some QI, USDC, SDT, MOCA, STACK for ETH through 1inch; exchanged 39,357.25 sdam3CRV to 43,910.09 amDAI. The attacker’s address (0x157…090 ) currently has a balance of 11,016.60 MATIC, 507,930.87 MOCA, 2,707.91 ETH, and 43,910.39 DAI.
The attackers began dumping stolen QiDAO on Quickswap DEX with high slippage, resulting in a 65% drop in the price of the governance token. The Polygon community took advantage of the opportunity to buy the dip, allowing the governance token to rise to $0.6 after falling below $0.18.