In this article, we are going to talk about IOTA (Ticker: MIOTA). According to the whitepaper of IOTA, it is a cryptocurrency for the Internet-of-Things (IoT) industry. It provides a feeless platform with high scalability.
In Bitcoin, the major drawback was scalability. It can process seven transactions per second. The process of clubbing transactions into a block and solving the complex puzzle adds additional cost(called mining fees). It is unsuitable for micropayments as you may end up paying more. There can be a clash in the network because of distinguished designations like Miners and Nodes.
IOTA Architecture and Participants
IOTA doesn’t use blockchain; instead, it uses a Directed Acyclic Graph(DAG) structure called Tangle for storing the transactions.
The Tangle consists of sites and edges. The participants in the IOTA are called Nodes. They are responsible for issuing and validating transactions.
Sites are individual transactions in the network, and Edges are the connection to the previous two sites.
Tips are transactions that are yet to be confirmed. To make sure the network is operational, the IOTA team has introduced a Coordinator, which is like a centralized protocol that performs the same task as individual users.
It is important to note that IOTA is an asynchronous network. This means different nodes may have different data.
IOTA Transaction Validation
As mentioned earlier, IOTA is a feeless platform. So, the only way to do that is to get rid of miners.
You must be wondering how does the network operates without miners as they are responsible for verifying transactions.
IOTA came up with an innovative way to assure trust in the network as well as verify the transactions.
First of all, to issue a valid transaction, the node must solve a cryptographic puzzle. This is achieved by finding a nonce such that the hash of that nonce concatenated with some data from the approved transaction has a particular form.
Here the transaction and a nonce is converted to trits ( ternary numerical system), and it is then hashed using curl hash function.
For the transaction to be valid, the hash should end with the right number of zeros.Otherwise, the nonce is changed. It keeps going on until a hash is generated, which ends with the specified number of zeros.
Second, to include a transaction in the network, the node must approve any previous two tips. The tip selection is made through Markov Chain Monte Carlo (MCMC) algorithms.
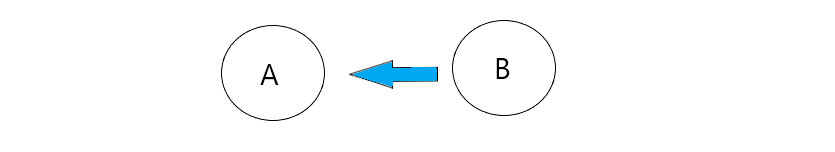
The approval can direct or indirect. In the case of direct approval, there is a direct arrow between two transactions. For example, B approves the transaction A.
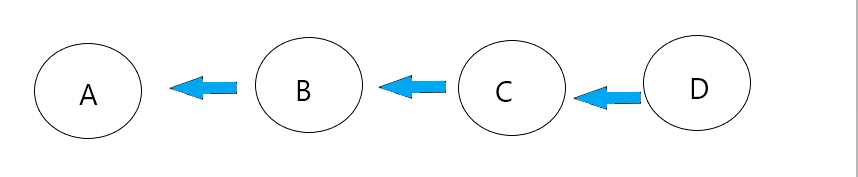
In the case of indirect approval, there is no direct arrow, but there is a path that has at least two transactions in it. For example, D approves transaction A through the path ABCD.
This feature makes IOTA highly scalable. As the flow of transaction increases in the network, so will be the approval of the transaction.
As a reward, the node’s transaction will be included in the network, and in the future, the new transactions will verify it.
This will increase the confidence of the network in the transaction. If the node finds an invalid or conflicting transaction, the nodes need to decide which transactions will become orphaned. The orphaned transaction will fall into oblivion.
Concept of Weight and Cumulative Weight
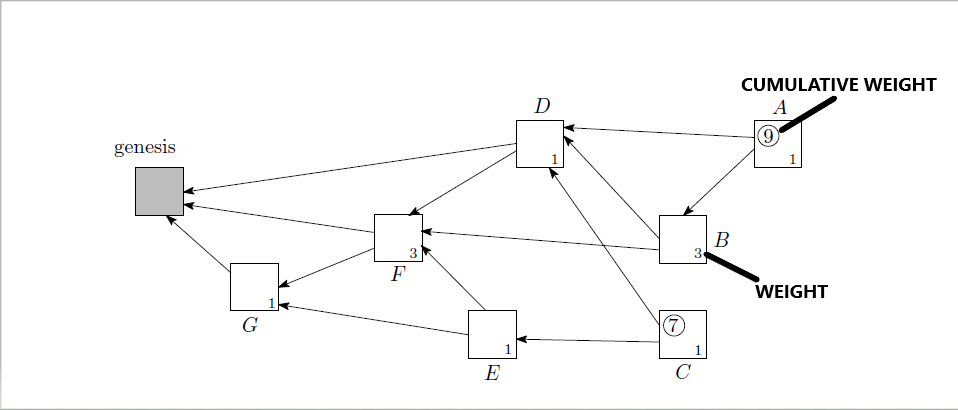
The weight of a transaction is proportional to the amount of work that the issuing node invested into it.
It is attached to the transaction, and it acts as proof that the transaction is valid.
It shows that some work was done by the user to show that the transaction is a valid one.
Transactions with large weights are considered as more important than the one with a small weight.
Cumulative Weight is defined as the sum of its own weight of a particular transaction and the weights of all transactions that directly or indirectly approve this transaction.
Sites with high weight usually have a high cumulative weight.
In the above diagram, The small number denotes weight, and the numbers in the circle indicate cumulative weight. Transactions A,B,C,E directly or indirectly approves transaction F. The cumulative weight of F is 3 (own weight)+ 1(A) + 3(B) + 1(C) + 1(E) =9.
IOTA’s Roadmap
Qubic: It is one of the promising features of IOTA. So, let us familiarize ourselves with some terms.
- Quorum is the minimum amount of vote needed to reach consensus in a distributed system.
- Oracle machines are external data providers to the Tangle.
- Sometimes, the computational processes are too intensive for a device to handle. In such cases, outsourced computation helps in distributing computational tasks.
- Smart contracts are deterministic programs that are executed when a specific condition is fulfilled.
According to the official definition,
What is IOTA Qubic?
Qubic is a protocol that specifies IOTA’s solution for quorum-based computations, including such constructs as oracle machines, outsourced computations, and smart contracts.
So, a Qubic is a manifestation of all of the above to make IOTA programmable, secure, trusted, incentivized, and, as said by founders, an IOTA-based world supercomputer.
- Improved networking: Research and development of a networking broker is on its way by IOTA that enables to switch between different networking protocols fluidly
- Automated Snapshotting: It will enable IoT devices to stay updated with the ledger without storing the whole ledger.
- Identity of Things(IDoT): The underlying idea to give an identity to the IoT devices. It includes it’s manufacture details and functionalities.
- Permanodes: Certain devices will need the whole ledger for their function. So, Permanode stores the entire Tangle history and data in it permanently and securely.
- Masked Authenticated Messaging(MAM): MAM allows devices to encrypt entire data streams and securely anchor those into the Tangle in a quantum-proof fashion. Only authorized parties will be able to read and reconstruct the whole data stream. It is similar to how modern communication systems except that it will be between devices in a decentralized fashion.
Application of IOTA
- Jaguar Landrover is using the IOTA Technology to pay drivers for car data.
- IOTA, Dell Technologies, and The Linux Foundation come together to create a project that verifies the authenticity of data coming from sensors.
IOTA is still in its development phase. Currently, they are working on a protocol that will make IOTA quantum attack free. The team is aiming to make IOTA more mainstream, secure, and decentralized by getting rid of coordinators.
- Shrimpy Review – Crypto Trading Bots for Social Portfolio Management
- Understanding Cryptocurrency Trading Bots [2020](Opens in a new browser tab)
- Ethereum versus Bitcoin
- What are Dapps? (An ultimate guide)
- Proposing Future Ethereum Access Control
- Building An Ethereum Simulation Game – Part 3 – The Front End
- Bitcoin ATM – Pros & Cons
- Commit Rank is now Activity Rank
- Cryptocurrency —Advantage, Disadvantage, and Risk
- ChangeNOW review – A reliable way to exchange crypto










