Key Takeaways:
- Crono’s DEX MM Finance faced a DNS attack on May 4.
- The hacker’s identity is still unknown.
- Users lost over USD 2,000,000 worth of virtual assets.
- The team is working towards a compensation package to reimburse the lost funds of the users.
Time and again, firms dealing with services related to digital assets have faced exploitation and rug pulls. This week, the Mad Meerkat Finance, the Cronos-based Decentralized Exchange, fell prey to a DNS attack and lost $2M.
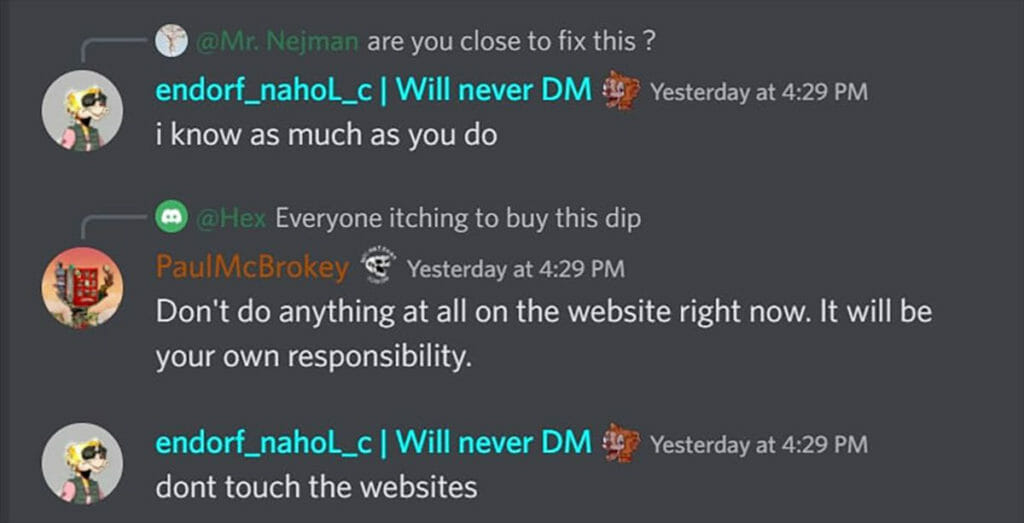
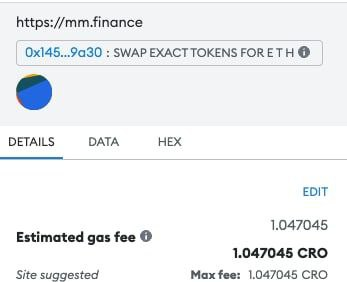
DNS exploits are a common sight in the crypto industry as it is easy to detect the vulnerabilities in the domain name system or DNS. A similar breach started happening in the front end of MM Finance around 7:30 PM UTC on May 4 and continued for 3 hours. All active users who were swapping, adding, or removing liquidity lost their Liquidity Provider Tokens (LPs) to the attacker’s address (https://cronoscan.com/address/0xb3065fe2125c413e973829108f23e872e1db9a6b). While it took some time for the team to take down the front end, they engaged with users over discord and advised them not to use the site for the moment.
The postmortem of the attack came a day after, but it is hard to gain any knowledge about the incident from the official post. It is yet to be found how the attacker gained access to the front end. However, the team updated on discord that over 600 transactions were rerouted to the attacker’s address, which was then bridged over to Ethereum before it was deposited into Tornado Cash.
The firm has expressed its regrets to customers for losing their funds and had promised to compensate its users. It has also released a four-step plan that users must follow before performing swaps to ensure security. They have also asked users to save the company’s router contract in their address book to avoid any confusion in the future.
There is another update from the MM Finance team, who has successfully tracked the financing supporter of the attacker to OKX, and all the smart contracts of the users are safe along with the MM Ecosystem tokens. However, they are still on the lookout to detect the hacker’s identity.









