Joe Grand is an electrical engineer and inventor who has been hacking hardware since he was ten years old. Known by the hacker handle “Kingpin,” he was part of the famed L0pht hacker collective that, in 1998, testified to the US Senate about a vulnerability that could be used to take down the internet or allow an intelligence agency to spy on traffic.
In a recent Tweet shared by Joe Grand, he said he has hacked Trezor and recovered $2 million. Replying to his Tweet, Trezor said that we want to add that the vulnerability was already fixed, and all new devices are shipped with a fixed bootloader. Thanks to saleemrash1d for his security audit.
In early 2018, Dan Reich and a friend decided to spend $50,000 in Bitcoin on a batch of Theta tokens, a new cryptocurrency that was only worth 21 cents at the time. They initially held the tokens with a Chinese exchange, but the Chinese government’s broad crackdown on cryptocurrency meant they would soon lose access to the exchange, so they had to transfer everything to a hardware wallet. Reich and his friend selected a Trezor One hardware wallet, set up a PIN, and then got busy with life and forgot about it.
By the end of the year, the token had fallen to less than a quarter of its original value, recovered, and then crashed again. Reich decided to cash out, but his friend had misplaced the paper on which he’d written the PIN and couldn’t recall the digits. They attempted to guess what they thought was a four-digit PIN (it was five), but each failed attempt doubled the wait time before they could try again. The data on the wallet would be automatically erased after 16 guesses. They came to a halt after a dozen attempts, afraid to go any further.
Reich gave up and mentally wrote off the money. He was willing to accept the loss unless the price began to rise again. The value of their tokens began to skyrocket from a low of around $12,000. It would be worth more than $400,000 by the end of 2020, briefly exceeding $3 million. It would be difficult, but not impossible, to gain access to the wallet without the PIN. And, with millions at stake, Reich and his friend vowed to find a way inside.
Reich and his friend were desperate to crack their wallet as the value of their inaccessible tokens skyrocketed in 2020. They searched the internet until they came across a 2018 conference talk by three hardware experts who discovered a way to access the key in a Trezor wallet without knowing the PIN. The engineers refused to assist them, but this gave Reich hope.
“We at least knew that it was possible and had some directional idea of how it could be done,” Reich says. Then they discovered a financier in Switzerland who claimed to have contacts in France who could crack the wallet in a lab. But there was a catch: Reich didn’t know their names and couldn’t go to the lab. So instead, he’d have to hand over his wallet to the financier in Switzerland, who’d then delivered it to his French as ociates. It was a crazy idea fraught with danger, but Reich and his friend were desperate.
COVID and lockdowns slowed their plans in 2020. Still, in February 2021, with the value of their tokens now $2.5 million, Reich was planning a trip to Europe when they discovered a better option: a hardware hacker in the United States named Joe Grand, and their hack journey started from here.
Reich, an electrical engineer who owns a software company, had a better ability than most to assess if Grand had the skills to pull off the hack. After a single conversation, he knew they’d found the right person. “I remember thinking, ‘Wow, this is perhaps one of the brightest electrical engineers I’ve ever met,“ he recalls.
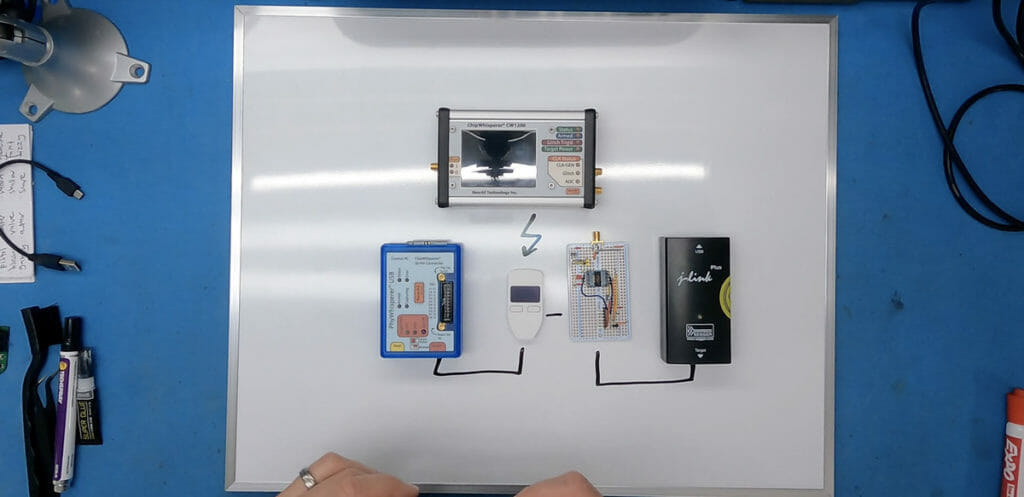
Grand, who has a custom lab in his family’s Portland backyard, bought several wallets identical to Reich and his friend’s and installed the exact version of the firmware. After that, he spent three months researching and attacking his practise wallets with various techniques. Finally, they agreed that Reich, who lives in New Jersey, would not fly to Portland with his wallet until Grand cracked three wallets using the same method.
Grand had previous research to g ide him. In 2017, a 15-year-old hardware hacker in the UK named Saleem Rashid had developed a method to successfully unlock a Trezor wallet belonging to tech journalist Mark Frauenfelder and helped him free $30,000 in Bitcoin. ashid discovered that when the Trezor wallet was powered on, it made a copy of the PIN and key stored in the wallet’s secure flash memory and stored it in RAM.
A vulnerability in the wallet allowed him to put the wallet into firmware update mode and install his unauthorized code on the device, allowing him to read the PIN and key where it was in RAM. However, when he installed his code, the PIN and key stored in long-term flash memory were erased, leaving only the cop in RAM. This made it a risky technique for Grand to use; if he accidentally erased the RAM before reading the data, the key would be lost.
As a result, Grand turned to the method used in Reich’s previous conference talk f om 2018. Despite Trezor removing the PIN and key that were copied to RAM during boot-up, the researchers discovered that the PIN and key were still present in RAM during anoth r stage. Furthermore, they discovered that the PIN and key were temporarily moved to RAM during the firmware update mode to prevent the new firmware from writing over the PIN and key, then returned to flash once the firmware was installed. As a result, they devised a method known as “wallet.fail.”
This attack used a fault-injection method, also known as glitching, to compromise RAM security and allow them to read the PIN and key while they were temporarily in RAM. In any case, Trezor had changed its wallets since then so that the PIN and key copied to RAM during boot-up were erased when the device was put into firmware update mode.
Grand discovered that the key and PIN were still copied to RAM when the device was po ered on in the firmware version installed on Reich’s wallet. Grand could read RAM and downgrade the security to RDP1 if he glitched the device at the right time. And, unlike the wallet. Fail scenario, because the key and PIN were only copied to RAM at this point and not moved, they remained in a flash if Grand inadvertently wiped the RAM. It was a much safer solution than cleverly drawing on both previous attacks.
The only issue was that the glitching required thousands of tries repeatedly powering up the wallet and using different parameters to affect the voltage to the microcontroller each time, in an attempt to hit the precise moment that would allow him to downgrade the microcontroller’s security. It took three to four hours to use an automated script, and there was no guarantee it would work on Reich’s wallet, even if it did work on the practice wallets. Reich compared the excruciatingly painful wait to sitting through a stakeout.
Grand wrote his programme so that if and when the glitch worked, his computer would exclaim, “Hack the planet!”. It was a reference to the 1995 film Hackers. Last May, when it came time to do the hack for real, Reich flew to Portland for two days. The first day was spent setting every hing up. They filmed the hack with a professional crew, and the next day, Grand launched his script.
They then sat and waited. The computer finally exclaimed, “Hack the planet!” after nearly three and a ha f hours. The key and five-digit PIN were visible on Grand’ screen. Reich and his friend had now amassed a $2 million fortune. He immediately transferred the Theta tokens from their account and paid Grand a percentage of the booty for his services. It was an exciting moment for Grand, not just because of the money on the line.
“It kind of reinvigorated me… and helped me decide what I should be doing with my skills,” Grand said. Trezor has already addressed a portion of the issue Grand exploited in later versions of its firmware. Wallets no longer copy or move the key and PIN into RAM Instead, SatoshiLabs, which makes Trezor wallets, according to Pavol Rusnak, co-founder and CTO, now stores them in a protected part of flash that isn’t affected during firmware upgrades.