Key Takeaways:
- ETHW Core has just released the second code upgrade.
- EIP-155 is in effect.
- All transactions must now be signed with the Chain ID as of this release.
On August 23, the Ethereum fork project EthereumPoW (ETHW) announced that the second code update to enforce EIP-155 had been released. Following this upgrade, all transactions must include the chain ID. This will protect ETHW users from ETHPoS and other forks’ replay assaults.
This effectively protects ETHW users from replay attacks from ETHPoS and other forks, making ETHW the most secure chain following The Merge.
With this functionality enabled, ETHW users will no longer be vulnerable to replay attacks, i.e., buying/selling your favorite BAYC on ETHW will not be replayed on ETHPoS. This is by far the greatest safeguard, but ETH has not enforced it for understandable reasons.
The contract freezing feature has been moved to a new branch, and all integration and testing have been completed. The Core meeting on September 1st will decide whether this feature will finally be merged into the main branch.
Previously, the first version of ETHW Core included removing the difficulty bomb, updating EIP-1559, and adjusting the ETHW mining difficulty.
According to EthereumPow.ETHW Core will provide liquidity pool freezing technology to safeguard user assets and issue three batches of freezing lists totaling 121 contracts.
Ethereum will be PoS following the Merge. Some miners, however, may continue to mine on a dormant PoW split of Ethereum.
Unless miners can coordinate and agree to run their new PoW-only release of the Geth client with a new chain ID before the Merge, it will be feasible to “replay” transactions made on one side of the split onto the other. Anyone, at no expense, can do this to your transactions.
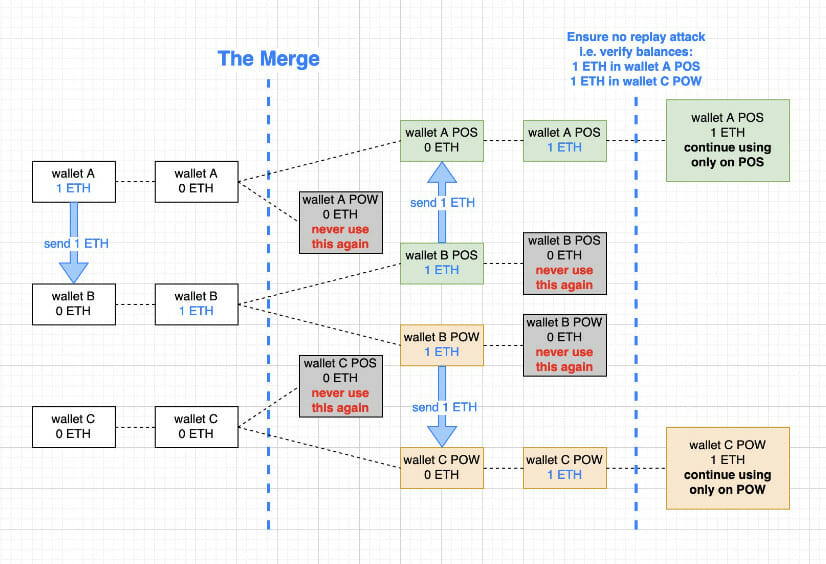
This means that if you try to sell your Eth or other assets on the PoW fork, you may also lose your actual Eth or other assets.
https://old.reddit.com/r/ethfinance/comments/wgiabm/the_risks_of_interacting_with_prospective_pow/
What exactly is a Replay attack?
A Replay assault is also known as a man-in-the-middle attack. It occurs when a hacker or malicious actor connects, intercepts, and modifies data on a protected network in order to delay or repeat the data/transaction to the prejudice of the originator. Replay attacks can occur in the blockchain space as well, particularly during chain splits or hard forks.
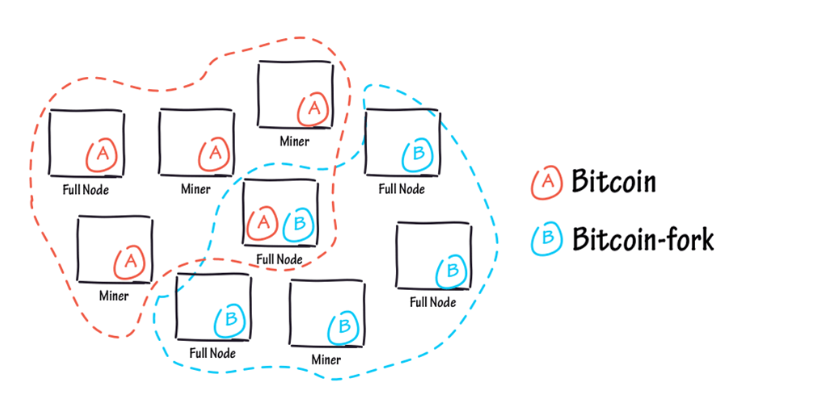
Replay attacks are common in the blockchain context, especially during hard splits like Ethereum 2.0. Hard forks are when an existing ledger is split in two, one with legacy software and the other with the divided version (ETH 2.0 Context). They can, however, be used to create new coins.
Entities can also use replay assaults during these forks. This is because every transaction made by someone whose access was legitimate before to the hard fork is likewise made on the Eth PoS chain.
This also implies that the transaction was done to circumvent blockchain security by repeating the transaction and having the same similar unit on another account (e.g. hackers account).