Key Takeaways:
- Crosswise hacked leading to the loss of $879K.
- PeckShield Inc. Tweeted and informed people that they have located the root cause behind the crosswise hack.
Today PeckShield Inc. tweeted and informed people that they had located the root cause behind the crosswise hack. According to PeckShield Inc., crosswise was exploited in, leading to the loss of ~$879K for the protocol.
Crosswise also informed people about it on their official telegram group. They wrote, dear Community, it seems someone attacked our token about an hour ago, dumping the price drastically. We do not know precisely what happened and need some time to address it. Such an attack should not have been possible, and we need time to figure this out. So please do not trade the token for the moment.
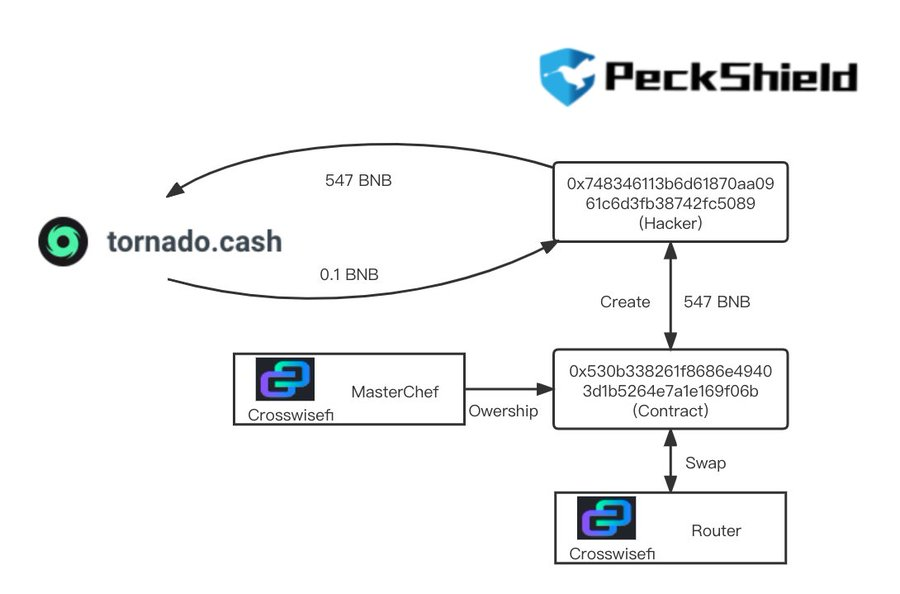
The hack was made possible due to the public exposure of a privileged function, which is then exploited to set the trusted forwarder and further hijack the owner privilege of crosswisefi MasterChef. The hacker calls the setTrustedForwarder() function to change TrustedForwarder, which transfers the ownership to the hacker.
The hacker then swapped 0.01 WBNB to 3.71 CRSS via a Crosswise router. The hacker then deposited 1 CROSS to Crosswisefi Masterchef. Then the hacker set the strategy to a new one under the hacker’s control and withdrew 692K CRSS from MasterChef. The hacker then swapped 692K CRSS to 547 WBNB. The initial funds to launch the hack are withdrawn from TornadoCash. The resulting gains are washed via TornadoCash.
They even said on their official telegram group that they would fix this, and indeed, this is NO RUG. This will take some time to address correctly, so do be patient. They informed people that their funds would remain safe and continue to farm and stake. They have asked people to not buy $CRSS until further notice to avoid the attack repeating.










