Key Takeaways:
- Tinyman AMM from Algorand was exploited for $3 million. After exploiting a previously undisclosed vulnerability in their smart contracts, some “unauthorised users” broke into some of the protocol groups.
- The attack resulted in the loss of certain ASAs in the early hours, according to the official blog post. As a result, there was a lot of volatility. The attack activated Tinyman’s wallet addresses and deposited a seed fund for the breach.
- The culprits effectively targeted the groups and began trading a percentage of their assets for newly generated group tokens to carry out the attack.

According to a blog post, Algorand’s decentralised purchasing and selling decomrum, Tinyman, was assaulted on January 1, 2022. The attacker took advantage of a flaw in Tinyman’s intellectual contracts, allowing some swimming pools to be hacked. The total amount of money lost is estimated to be around $3 million.
According to the announcement, the attack prompted “a drain of some ASAs in the first hours of the strike, which contributed to heightened volatility in the immediate aftermath.” The investigation is still ongoing, and the team has promised to pay anyone who has been damaged.
Tinyman apologised for the incident and promised that all affected users would be compensated and that the team was working on compensation plans. However, due to the permissionless nature of the contracts, he stated that they would be unable to impede any form of transaction on the blockchain.
Tinyman asked liquidity providers to withdraw all of their liquidity from any contracts related to the protocol to reduce the severity of the harm. In addition, to protect the community, all liquidity paths in the online application were closed and replaced with warning signals.
According to the crew, the perpetrators activated their pockets’ addresses and deposited a basic chest bombard. Then, they began concentrating on complexes and transferring money in exchange for blessing symbols.
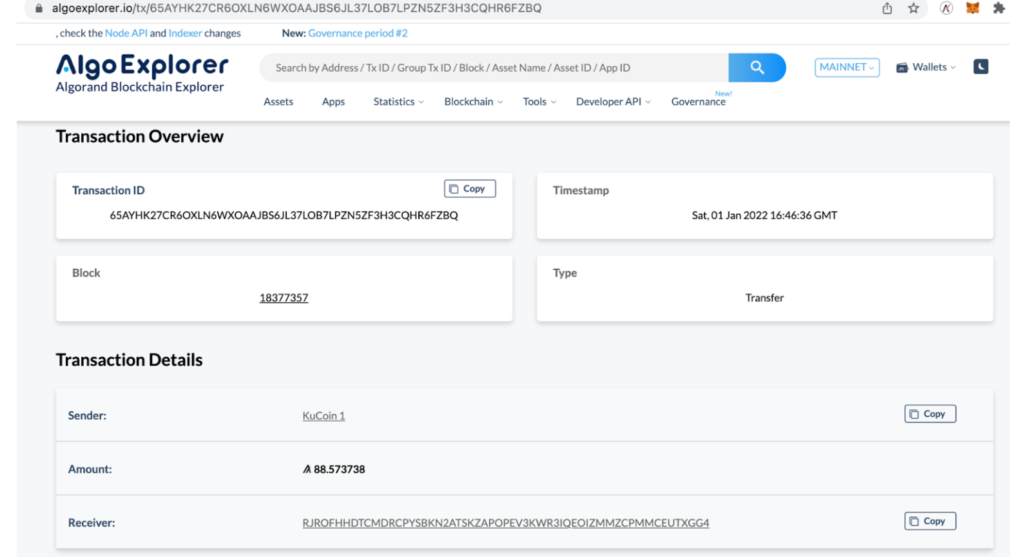
They started trading with the targeted pools to carry out their attack and swapped some of their cash for ASA ID: 386192725 (gobtc) and Pool Tokens. The attackers had ensured that they had the first cash to launch their hacks up until this point.
This transaction group was the account’s first target:
By burning these Pool Tokens, the attackers could obtain two of the same item rather than two different goods. According to the team, the assailants carried out the attack in this manner, stealing $3 million.
Transactions cannot be reversed or blocked since Tinyman is an entirely decentralised protocol. According to the research, Tinyman users should instead take liquidity from contracts. Tinyman’s entire liquidity has plummeted from $43 million before the attack to $20 million.
Because the contracts are permissionless, no one, not even the Tinyman team, can stop any transaction on the blockchain. Therefore, as a first step, on January 2, 2022, an official notice was sent to all Tinyman users advising them to withdraw all of their liquidity from any Tinyman-related contracts. In addition, all liquidity route additions in the web app were removed, and necessary warnings were posted on the website to protect our community.
Total liquidity in Tinyman was around 43 million USD when the attack started, but it quickly dropped to around 20 million a few hours later. Due to our suggestion, projects and users have started reducing their liquidities, bringing the total down to $5 million.
Due to the sheer affluent inflow of capital, attackers increasingly focus on the DeFi market, necessitating audit and insurance coverage solutions. The most significant funds were taken from the DeFi market in 2021, and it does not appear that the pattern will be sluggish in 2022.