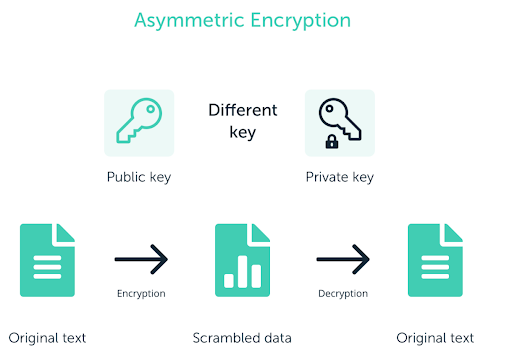
Encryption is a method of protecting digital data that involves the use of one or more algorithms and at least a key. The public and private keys form a part of a wider domain of cryptography, which is Asymmetric Encryption or Public-key Cryptography. They are of great importance in cryptocurrency.
Table of Contents
Summary
- Symmetric Encryption is single-key encryption.
- Asymmetric Encryption uses 2 different keys for encryption and decryption.
- The public key is used for encryption and the private key for decryption.
- The public key is not the bitcoin address.
- Don’t share your private key.
What is meant by Symmetric Encryption?
Symmetric encryption is also called single-key encryption as in symmetric encryption, there is only one key for both purposes, encryption, and decryption. Further, this is a very handy method to encrypt and decrypt things as it is very easy and basic.
What is meant by Asymmetric Encryption?
In regular or standard ways of encryption, we use a single key to encrypt and decrypt the document, whereas, in Asymmetric encryption or public-key cryptography, it is a completely different process whereby there are different keys to encrypt and decrypt the document. The idea behind Public Key Cryptography is to change from one form to another as easily as possible, meanwhile making it unrealistic to reverse the action, including a hidden thing without revealing any information.
The final result is a one-way mathematical operation, making it suitable for confirming the integrity of anything (like a transaction) as it is not alterable. In this method of encryption, we use a key named as Public key to encrypt the document and another key named as the private key to decrypt the document.
As their names suggest, we can reveal our public key to people as it is only used to encrypt the document, and we have to keep our private key unrevealed as it is used for decrypting the data and we can even find our public key with the help of our private key.
What are Public and Private Keys?
Private Key
A private key is generally a set of characters chosen at random. It is used to claim the rights of the bitcoin address related to that private key and to spend the money affiliated to that bitcoin address. This key must be kept safe and unrevealed along with a backup as if it is lost, then it can not be regenerated or reclaimed, and all the affiliated money would be gone.
Public Key?
The public keys are generated from the private key by a one-way trapdoor function, which means we can not get to the private key through the public key. Therefore, the public keys can be used to receive cryptocurrency. A person must keep their private key only to themselves. Losing it can be a heavy loss.
How is the Bitcoin address different from the public key?
We get bitcoin addresses from the public keys by applying one-way cryptographic hashing. Generally used algorithms for this purpose are SHA (Secure hash algorithm) and RIPEMD (RACE Integrity Primitives Evaluation Message Digest), particularly SHA256 and RIPEMD 160. Just like public keys, sharing your bitcoin address will cause no harm.
Public and Private Keys: Conclusion
There are 2 basic types of encryption, Symmetric and Asymmetric. Symmetric encryption uses one key for both purposes, encryption and decryption. Asymmetric encryption has one key for each purpose, the public key for encryption and the private key for decryption. The Bitcoin address is not the same as your public key. Therefore, you should restrain yourself from sharing your private key.
Frequently Asked Questions
1. What is the difference between Public and Private Keys?
The private key is used to encrypt the document decrypted by the public key; in other words, we can say that the private key is used to open the door that was locked using the public key.
2. How do I find my Public Key?
The public key is provided to you in most of the wallets, but not in all. The public key is used in compressed form in the address where you deposit your coins or the address where you receive your coins.
3. How do I find my Private Key?
Not many wallets allow you to export your private key, and in others, seed phrases are given to you to remember. This seed phrase is actually a decoded form of your private key, but you can’t derive the private key from the seed phrase.
Also read,